Sensors | Free Full-Text | Continuous Quantitative Risk Management in Smart Grids Using Attack Defense Trees
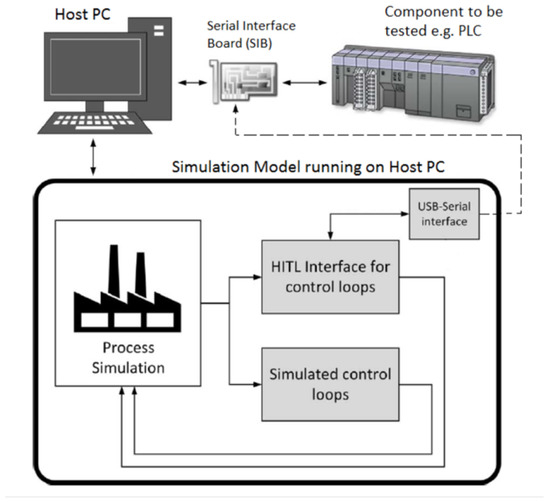
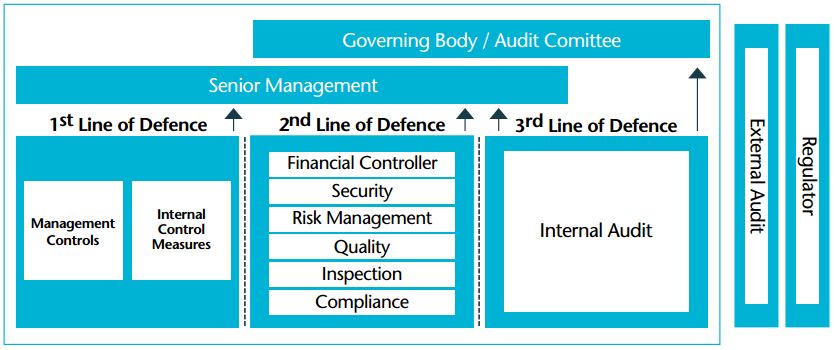
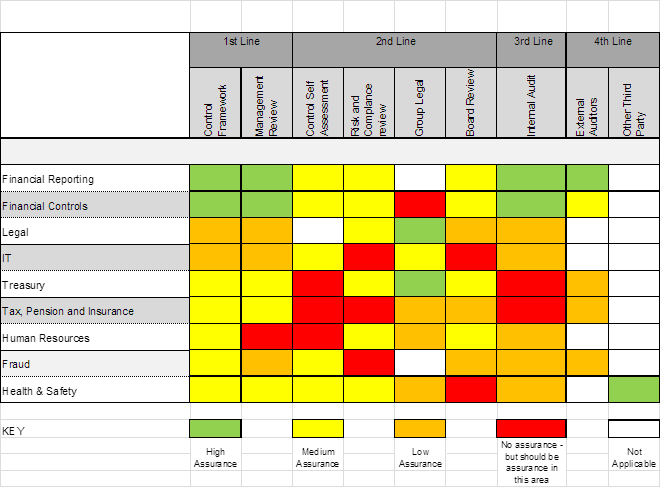
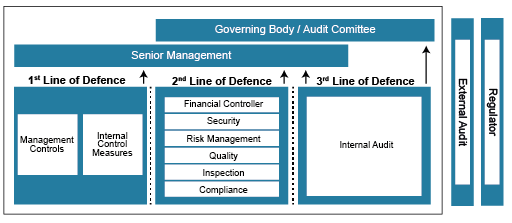
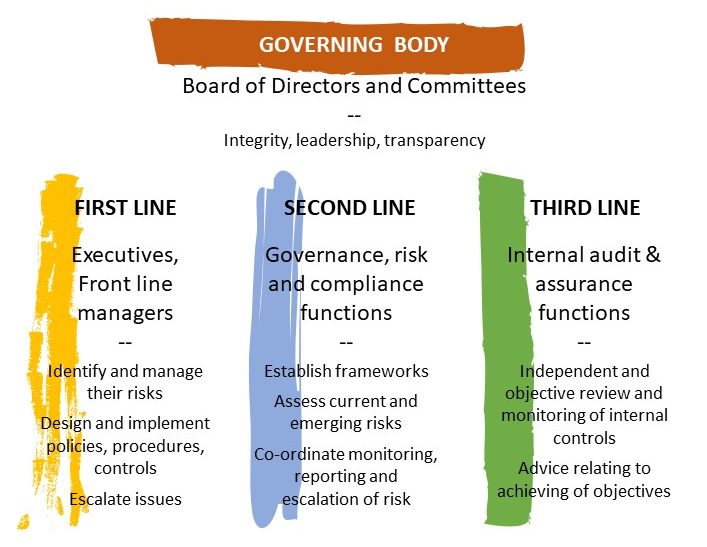
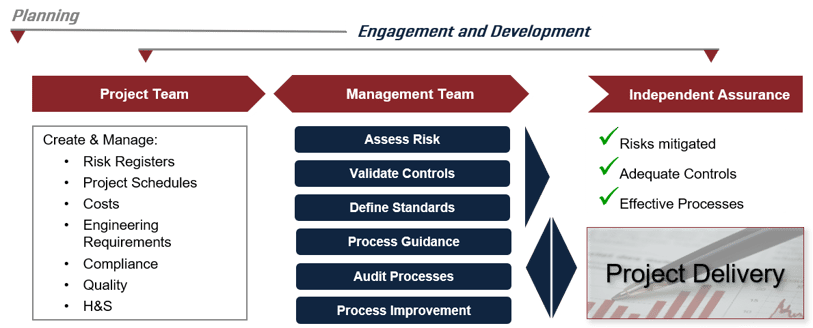
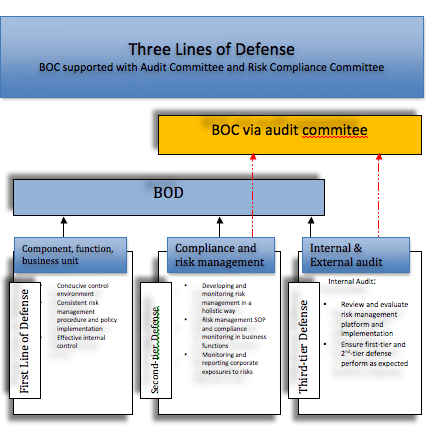
JSAN | Free Full-Text | Preliminaries of Orthogonal Layered Defence Using Functional and Assurance Controls in Industrial Control Systems