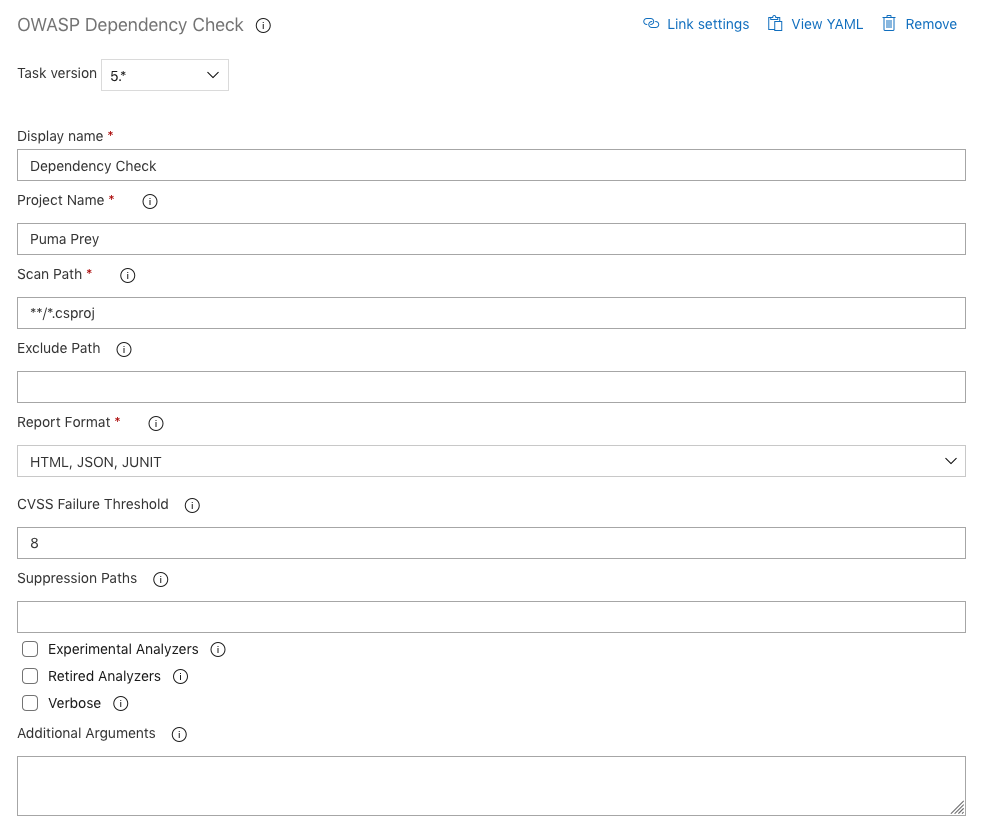
Enhancing Software Security: Leveraging OWASP Dependency-Check Scans for Proactive Vulnerability Management in CI/CD Pipelines | by Ramkrushna Maheshwar | Medium
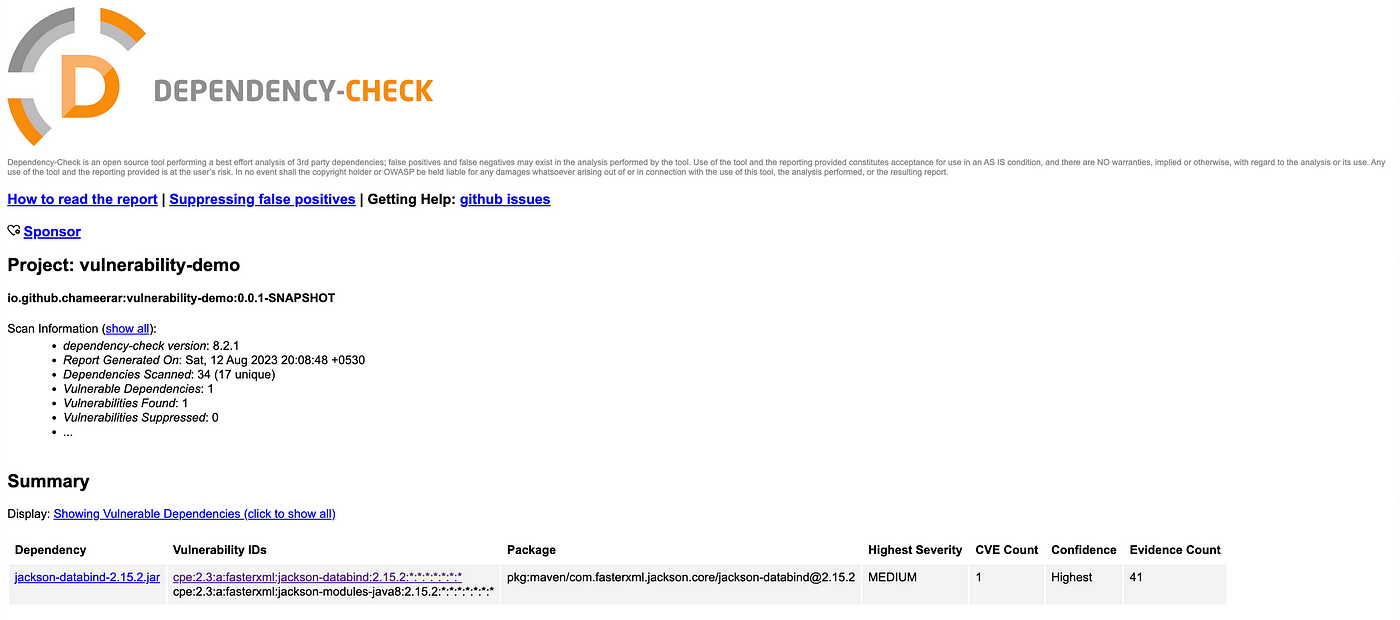
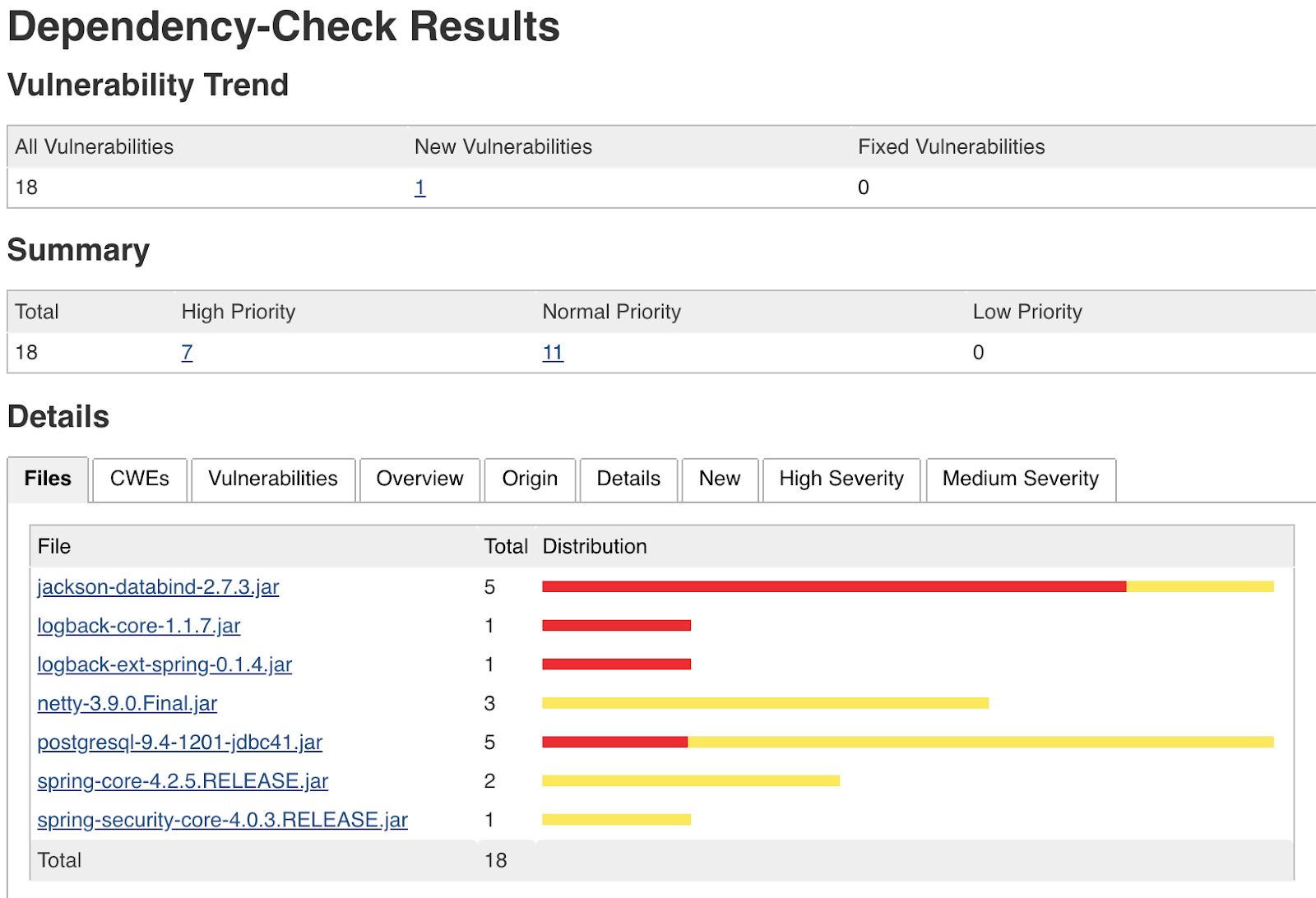
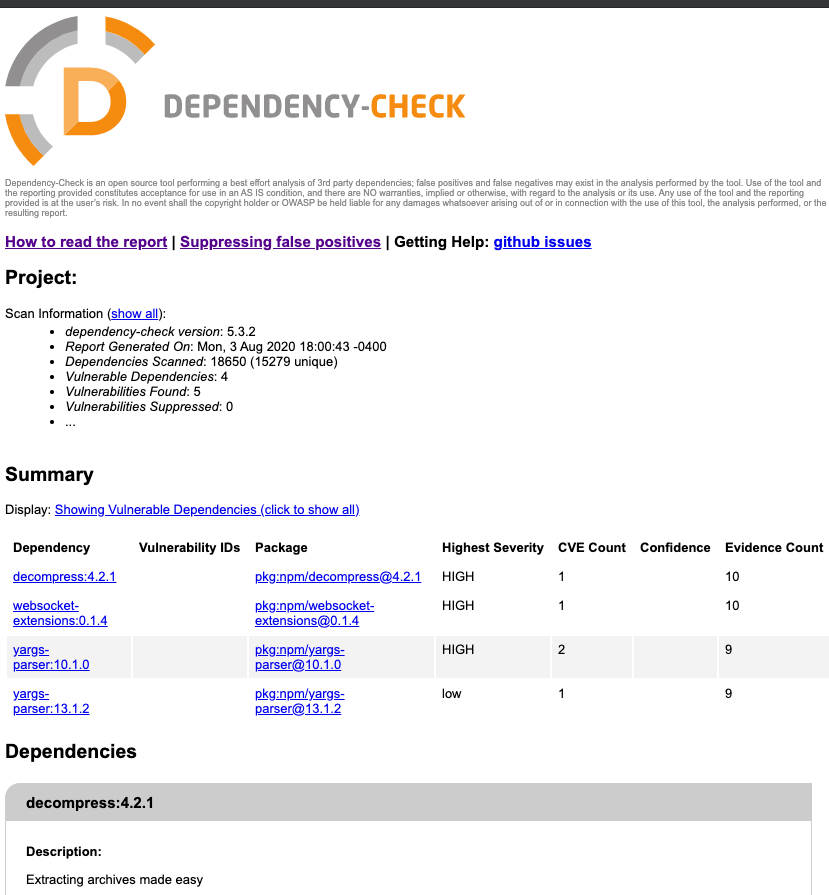
Find Vulnerable Dependencies using OWASP Dependency Check | by Chameera Rupasinghe | System Weakness
DependencyCheck v3.3.1 - A Software Composition Analysis Utility That Detects Publicly Disclosed Vulnerabilities In Application Dependencies
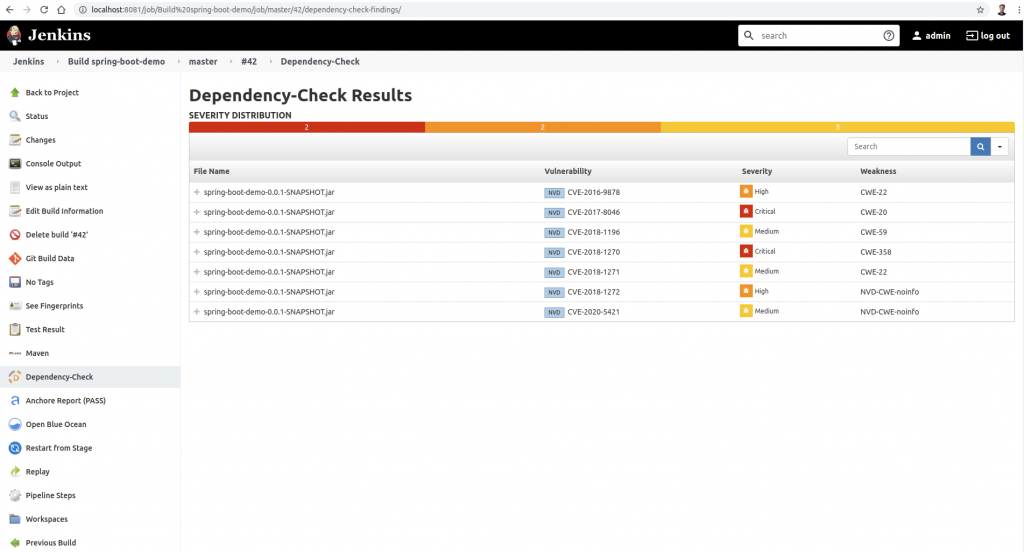
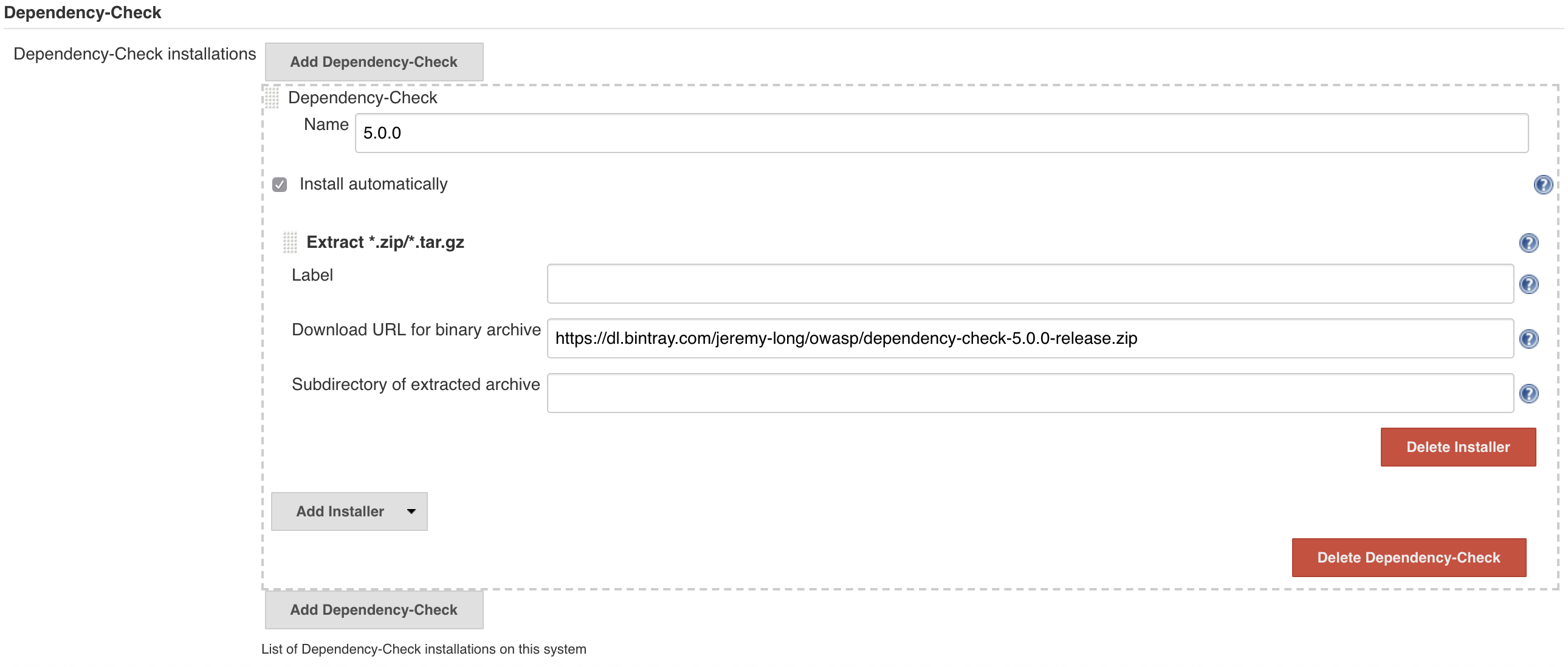
Automatically Scan Your Project Dependencies for Vulnerabilities Using Docker, Jenkins (Part 2/2) | HackerNoon
GitHub - dependency-check/dependency-check-gradle: The dependency-check gradle plugin is a Software Composition Analysis (SCA) tool that allows projects to monitor dependent libraries for known, published vulnerabilities.
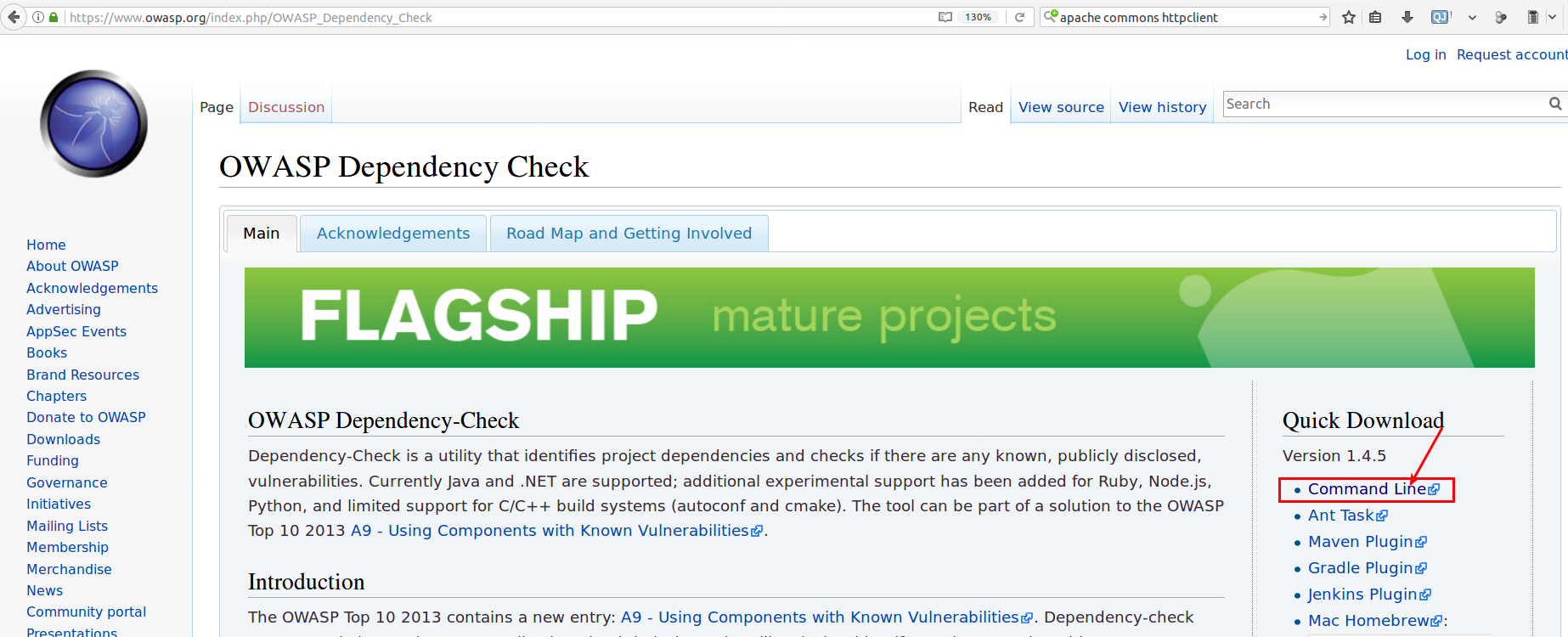
SECURITY INTERNAL . COM: OWASP Dependency Check CLI - Analyzing Vulnerabilities in 3rd Party Libraries

Online Course: Supply Chain Risk Management with OWASP Dependency-Check from Pluralsight | Class Central
.png)